Abstract
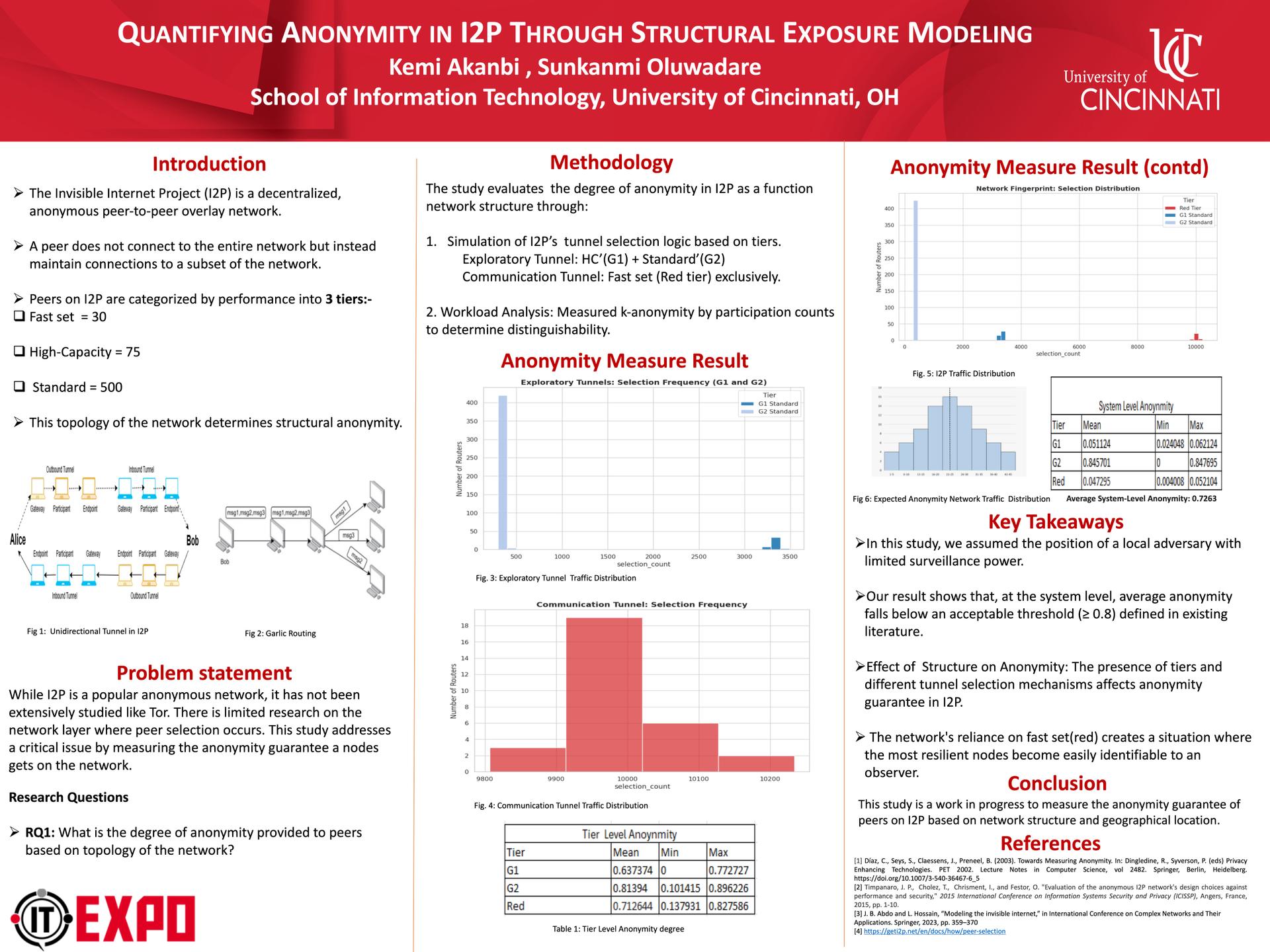
The Invisible Internet Project (I2P) is a decentralized anonymity network that routes user traffic through peer-selected, multi-hop encrypted tunnels. While I2P's goal is to prevent network observers from correlating user identity with online activity, the protocol's reliance on profiling peers for tunnel creation introduces potential topological vulnerabilities. The degree to which structural exposure undermines the anonymity guarantees of I2P is not fully understood. This study aims to quantify the anonymity level within I2P by applying structural exposure modeling to map tunnel selection paths against a defined local adversary model. The objective is to determine if I2P consistently meets the theoretical k-anonymity threshold necessary to obscure user identity from a localized observer. Our analysis demonstrates that I2P's tunnel selection bias significantly degrades the structural anonymity of the network, leaving users vulnerable to localized de-anonymization attacks.
Author: Kemi Akanbi