Abstract
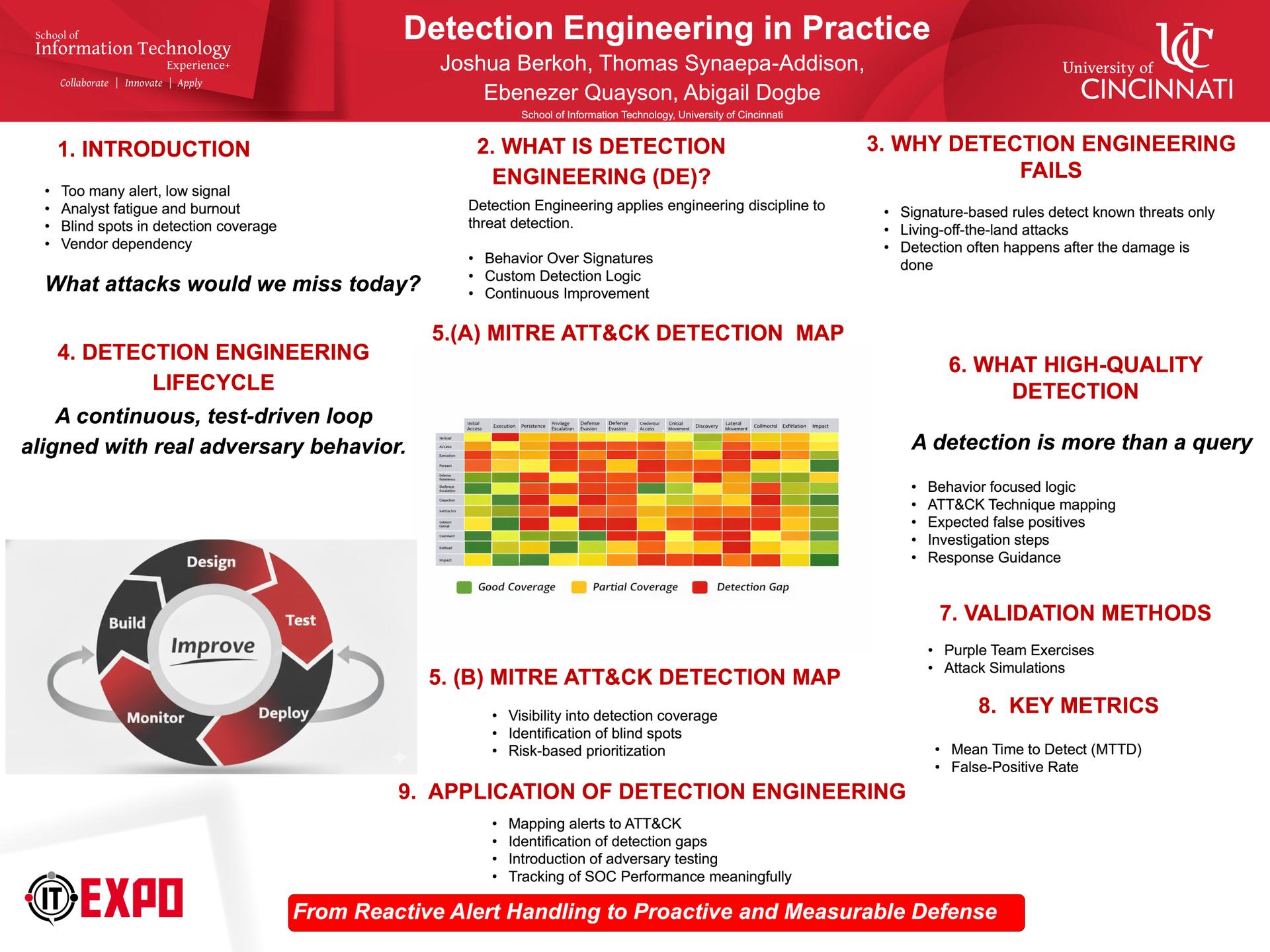
Modern security operations centers (SOCs) are overwhelmed by alert fatigue and persistent blind spots, largely due to inefficient detection engineering. Too often, teams rely on vendor-provided, untuned rules that generate excessive false positives or fail to detect sophisticated adversary behaviors. This poster presents a practical framework for detection engineering focused on a continuous, test-driven loop aligned with the MITRE ATT&CK framework. We distinguish between a simple query and a high-quality detection, which must include validated ATT&CK mapping, context-rich alerts, and actionable response guidance. We outline the process of hypothesizing, building, tuning, and validating detections through purple teaming and attack simulations. Implementing this structured methodology reduces Mean Time to Detect (MTTD), minimizes false positives, and shifts SOCs from reactive alert chasing to proactive threat hunting.
Authors: Joshua Berkoh; Thomas Synaepa-Addison; Ebenezer Quayson; Abigail Dogbe